Our staff has given numerous talks at WordCamps and meetups about WordPress security, and we have always claimed that WordPress is secure by default. All users really need to do is follow good password hygiene. WordPress is not like Windows – you don’t need to install virus scanners or security plugins right after installing WordPress. WordPress is not inherently insecure.
With all the myths and false advice out there, we recommend checking out our WordPress Security 101 presentation for a good introduction to WordPress security.
Despite our strong belief that WordPress in itself is secure, we recently decided to slightly adjust our approach in regard to a few specific issues in WordPress.
Introducing New Security Settings at Seravo
In the past year, several security companies have audited websites we run, and from their inspection checklists that contain hundreds of items, there are only a couple of minor things that often come up. While they don’t matter much, from a true security perspective, we want to help our customers get a 100 % compliance in these audits. That is why we have rolled out a new security section in our Seravo Plugin where users can harden their WordPress site with a few simple clicks using the following settings:
- Disable the XML-RPC API. Before WordPress had the WP REST API, there were some apps that communicated with WordPress using the XML-RPC API. Examples of apps that did this include Jetpack, pingbacks and the legacy WordPress Mobile app. XML-RPC API is a powerful beast and it allows, for example, doing lots of authentication attempts in parallel. It does not currently have any known security vulnerabilities, but some security experts still consider it as a potential security risk so it is frequently on security checklists. Since it isn’t needed on most sites, it can be disabled with a single click. Perfect for those who want to sleep their nights even better.
- Disable user enumeration in the WP REST API. As mentioned above, the new WordPress API system that arrived in WordPress in 2017 is nowadays preferred over XML-RPC. It is superior in many ways, but some people have privacy concerns about the API endpoint that lists the users of the site. The name of the author is typically visible on blog posts, so in most cases the list of authors is not considered a strictly matter, however in some scenarios it might be less than desirable for outsiders to be able to obtain a list of users on the site. The downside here is that turning off this endpoint usually breaks the Gutenberg editor’s author selection feature. But, fear not, for the way we implemented it at Seravo does not have any known downsides and the author selection feature functions perfectly normally.
- Disable author enumeration. Similar to the item above, some people dislike that in WordPress the website itself has by default listings of content by author, like example.com/author/joe or example.com/?author=123. Ticking this box will disable this functionality.
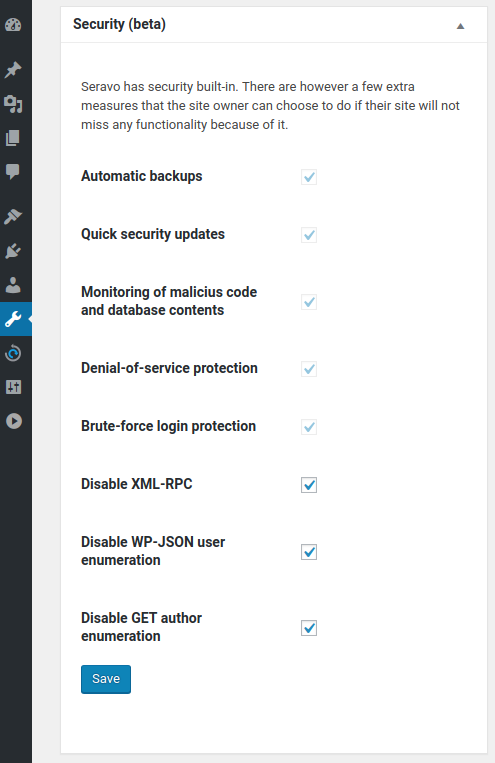
Since these items decrease the functionality of WordPress and may stop certain plugins or external features from working, we at Seravo do not want to have them disabled by default. However, with this security page in the WordPress admin area, we make it super easy for our customers to shut down these parts of WordPress if they want to do so.
Seravo Has Always Been Serious about Information Security
As part of our upkeep we also handle the security of the WordPress sites we run for our customers. We don’t claim that security issues never happen – nobody can guarantee that – but what we do claim is that our security architecture is built from the ground up to exceed any industry standards, that our operational security standards are high and that our company-wide security training makes our systems a hard target.
In fact, we are backing up this claim by promising our customers that if their site gets hacked while being in our upkeep, we will clean up the site for free. That’s a promise that nearly no one else is comfortable making. For more information, check out the page about security at Seravo.